Project Overview
Address Resolution Protocol (ARP) spoofing is a common Layer-2 attack that allows an adversary to intercept network traffic by manipulating MAC address resolution. This project demonstrates how ARP spoofing can be performed within a virtual network created using Mininet, Open vSwitch, and the POX controller. By poisoning the ARP tables of two hosts, the attacker can become a man-in-the-middle and observe and manipulate network traffic between them. Packet captures are used to analyze how spoofed ARP replies redirect traffic and enable interception. Then I demonstrate how enterprise networks mitigate this attack using security mechanisms such as DHCP Snooping and Dynamic ARP Inspection.
Lab Architecture
This lab environment was built using Mininet and Open vSwitch. Three hosts were connected to a single Layer-2 switch controlled by a POX SDN Controller. The attacker host was placed on the same broadcast domain as the victim and target to allow for ARP poisoning.
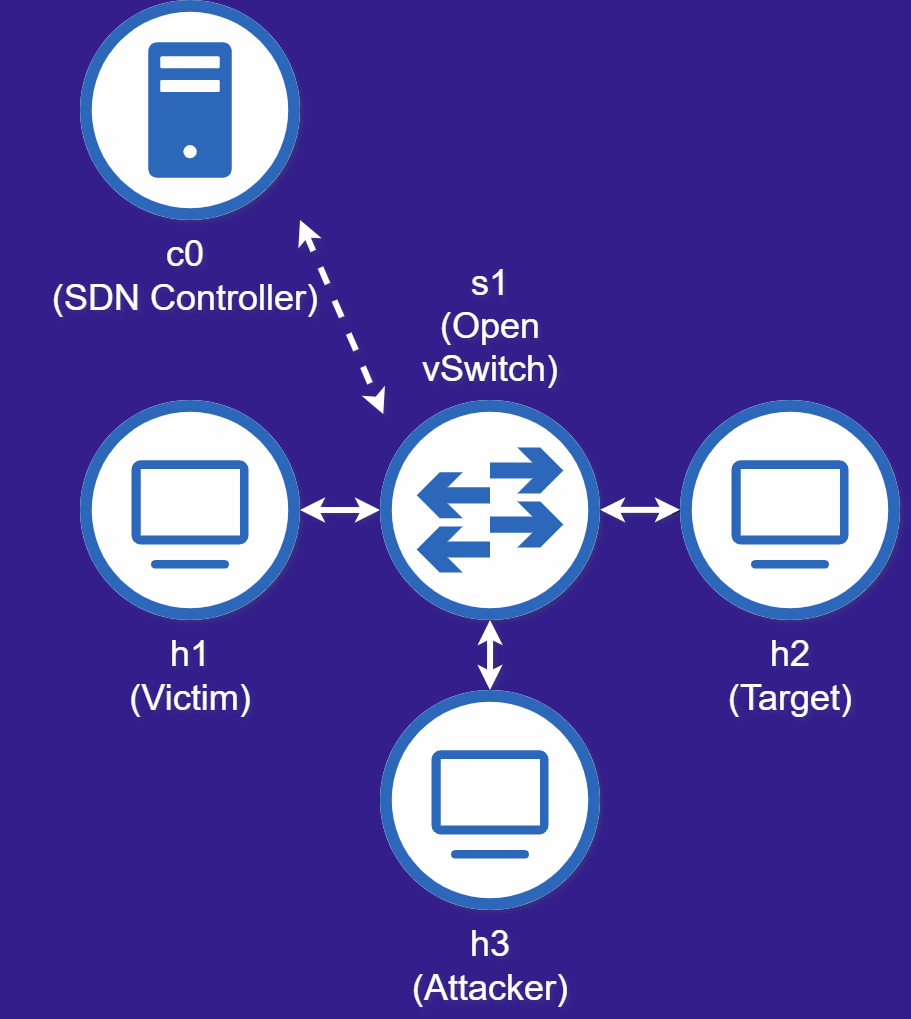
| Node | IP Address | MAC Address |
|---|---|---|
| h1 | 10.0.0.1 | 00:00:00:00:01:1e |
| h2 | 10.0.0.2 | 00:00:00:00:02:1e |
| h3 | 10.0.0.3 | 00:00:00:00:03:1e |
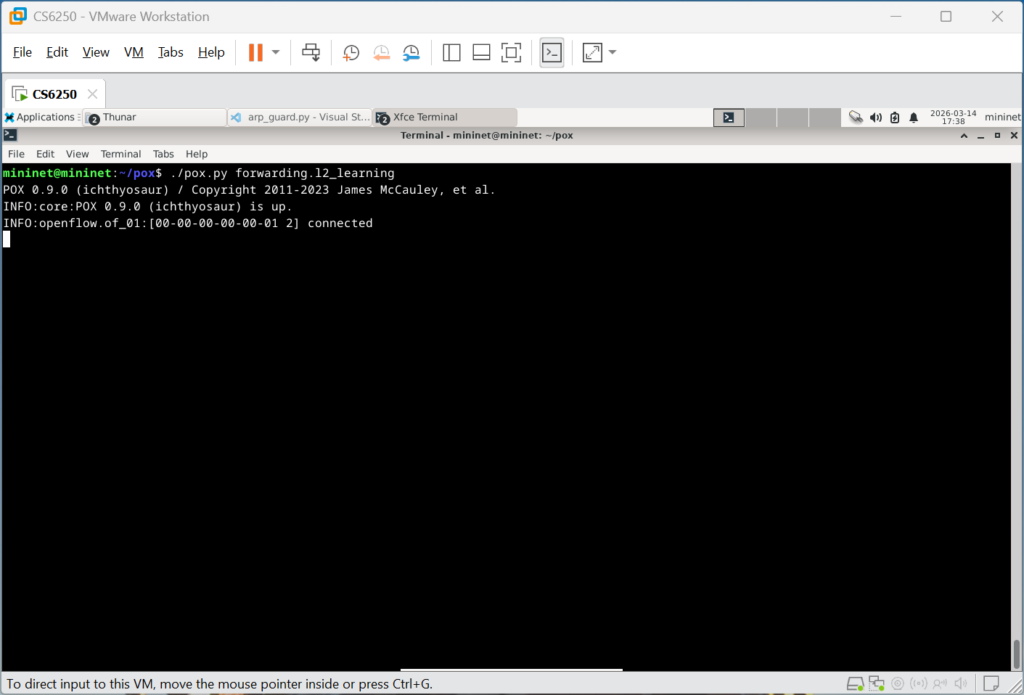
./pox.py forwarding.l2_learning
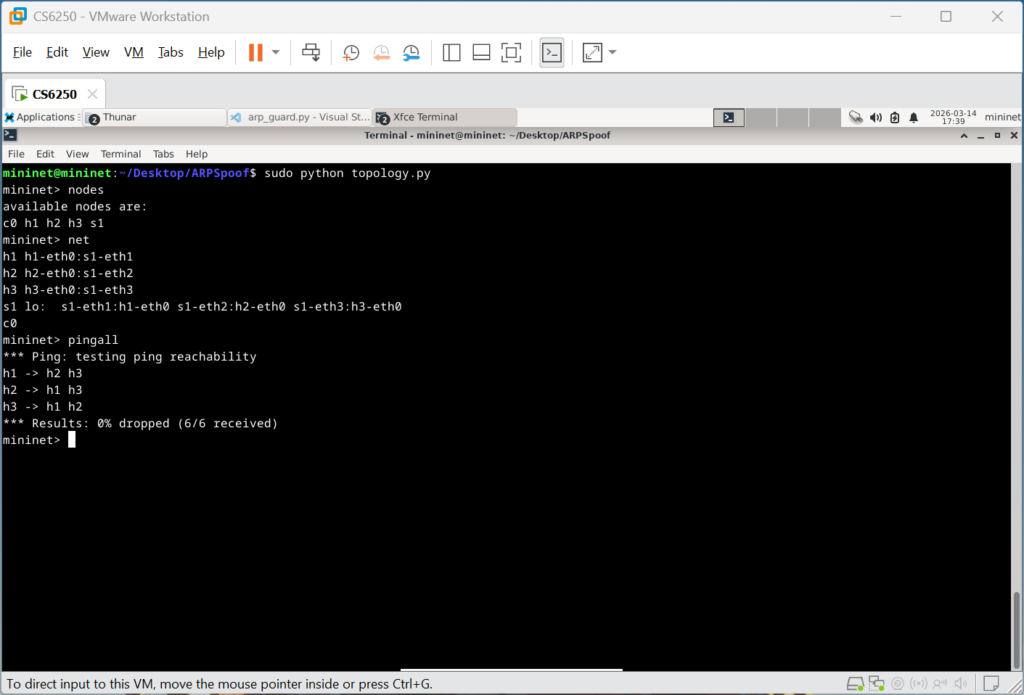
sudo python topology.pyThe Mininet topology was launched using a custom Python script, and the POX controller successfully established an OpenFlow connection with the virtual switch.
Attack Setup
To demonstrate ARP spoofing, normal HTTP traffic was first generated between the victim (h1) and the target server (h2). The attacker (h3) then launched an ARP poisoning attack to intercept communication between the two nodes.

h2> python -m http.server 80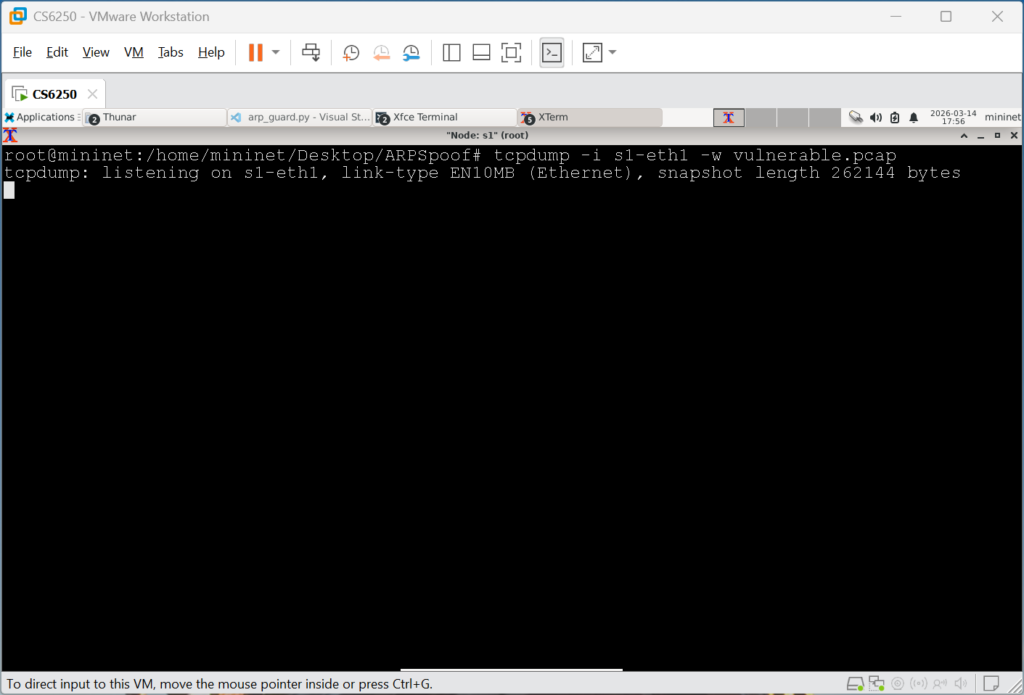
s1> tcpdump -i s1-eth1 -w vulnerable.pcap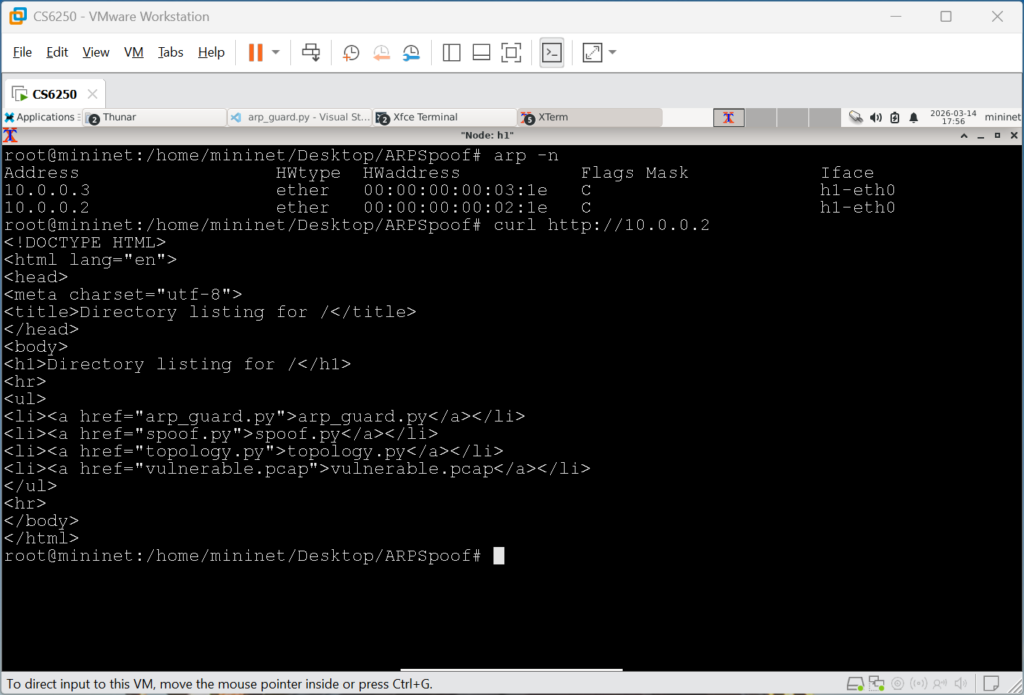
h1> arp -n
h1> curl http://10.0.0.2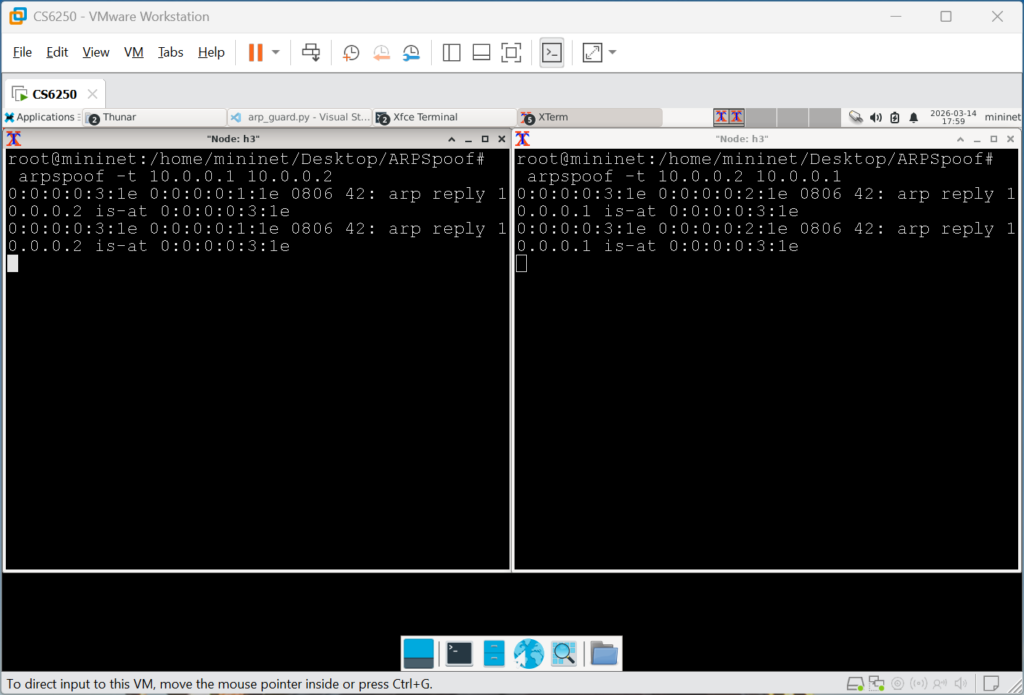
h3> arpspoof -t 10.0.0.1 10.0.0.2
h3> arpspoof -t 10.0.0.2 10.0.0.1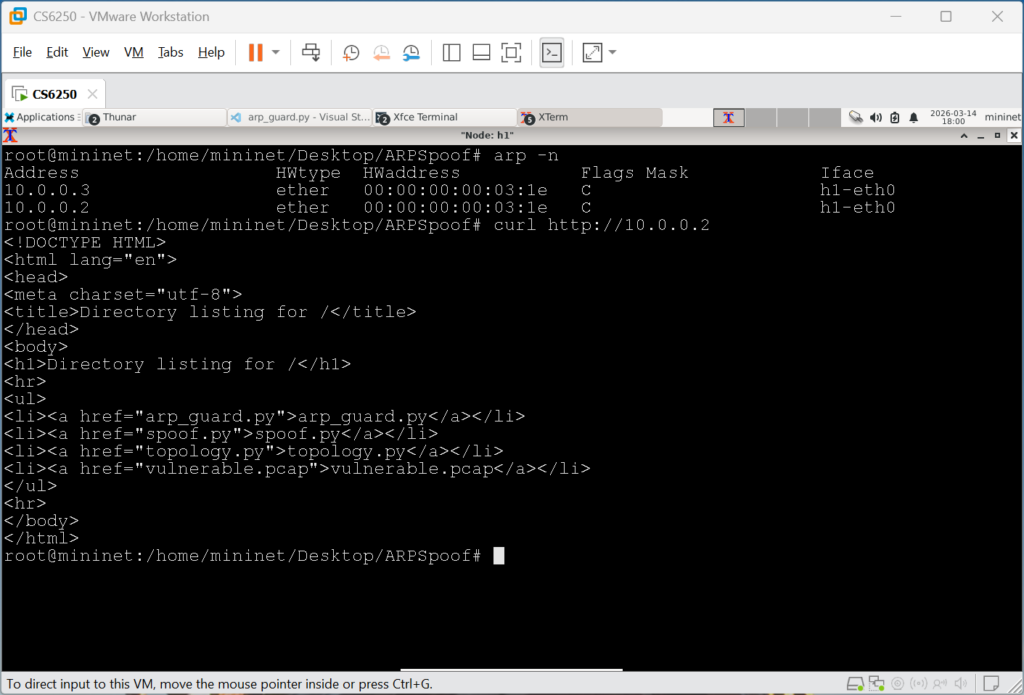
h1> arp -n
h1> curl http://10.0.0.2Packet Capture Analysis
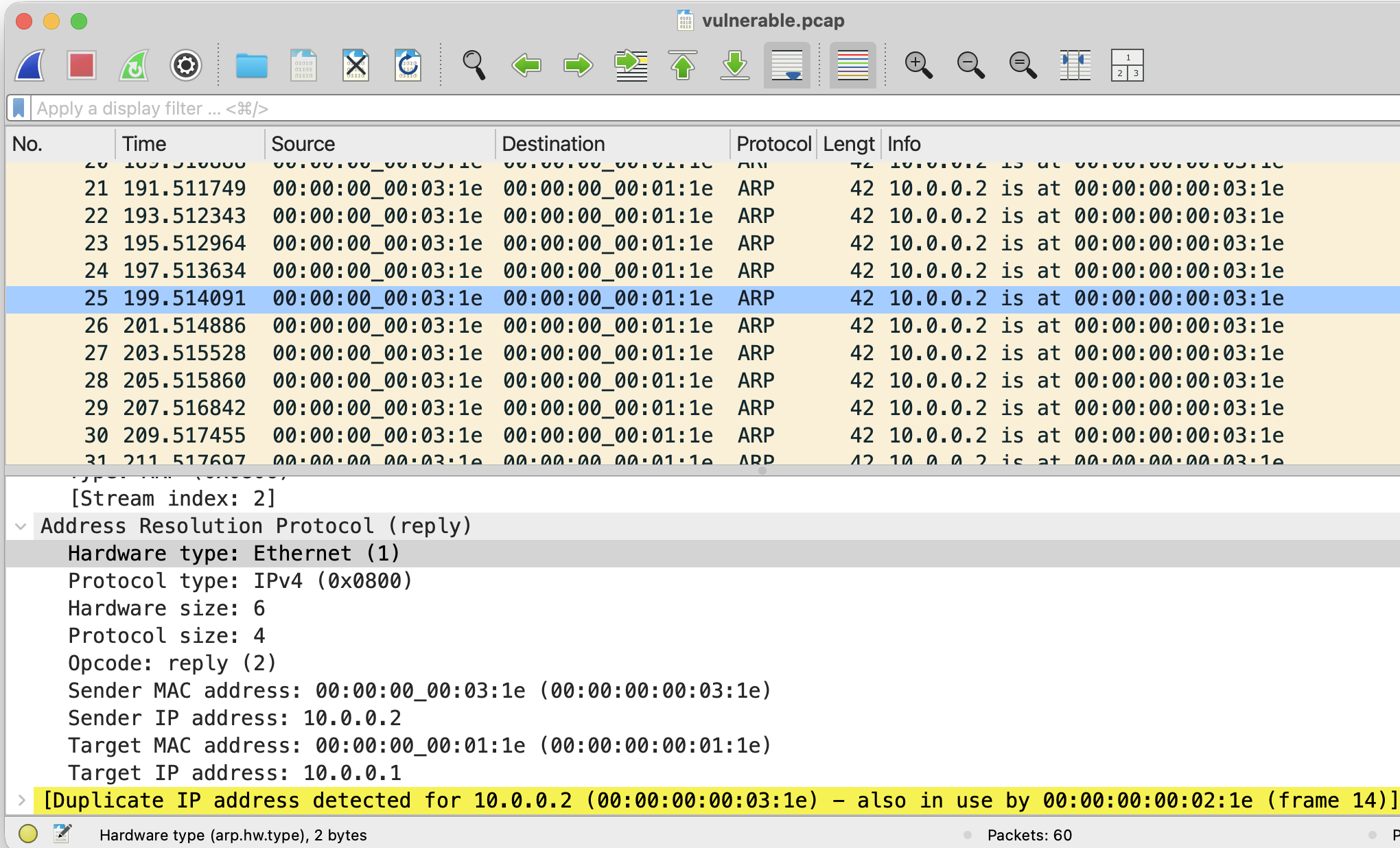
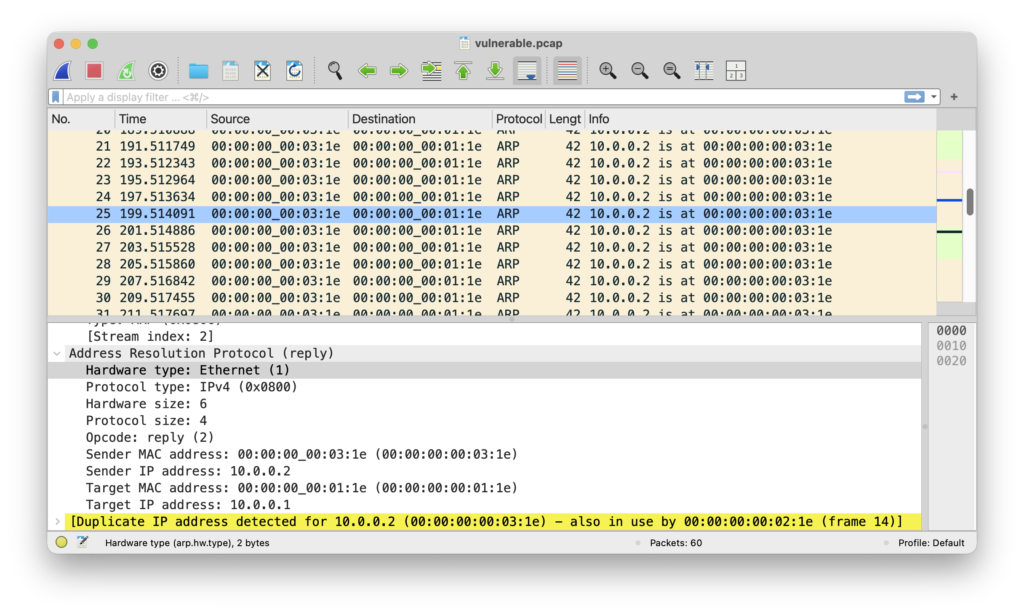
The Wireshark packet capture analysis shows that the attacker successfully spoofed ARP replies, claiming ownership of 10.0.0.2. As a result, the victim updates its ARP table and begins forwarding traffic to the attacker’s MAC address instead of the real host’s.
Attack Flow
The ARP spoofing attack works through the following steps:
- Normal communication
- The victim, h1, sends an HTTP request to the target, h2, and uses ARP to resolve the MAC address with the associated IP address 10.0.0.2.
- Attacker begins ARP poisoning
- The attacker, h3, begins sending spoofed ARP replies claiming that the IP address 10.0.0.2 is associated with its own MAC address (::03:1e).
- ARP table is now poisoned
- The victim, h1, receives the spoofed ARP reply, which associates the gateway IP address with the MAC address of the attacker.
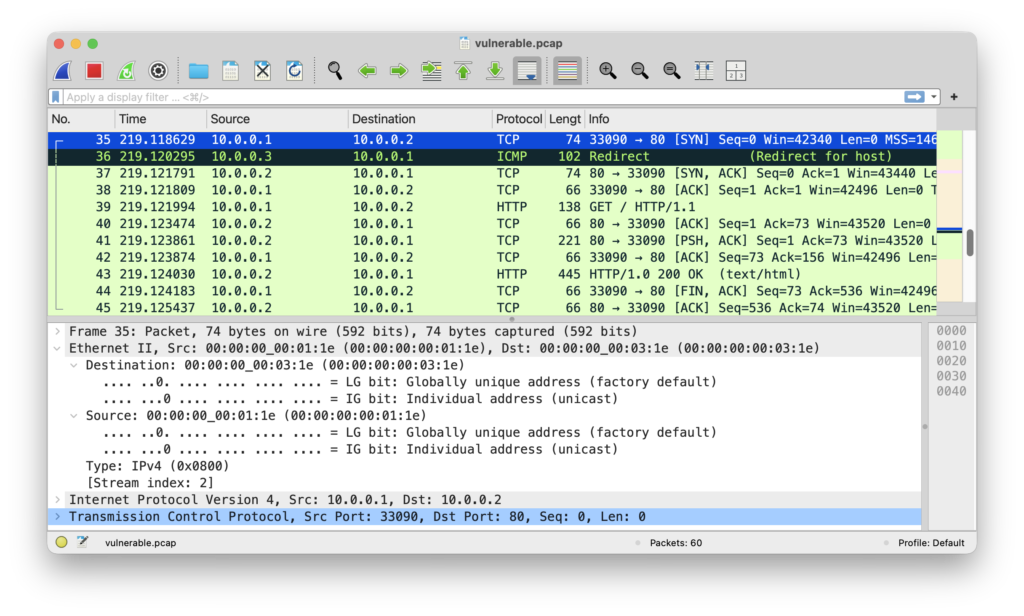
- Traffic is now redirected through the attacker
- Traffic intended for h2 is now sent to h3, allowing the attacker to intercept and forward packets.
- Man-in-the-middle established
- By enabling IP forwarding, h3 relays packets between the victim and target while eavesdropping on all packets between the two.
Security Implications and Mitigations
ARP spoofing can enable interception and modification of network traffic, usually with no visible indication to the affected victim. This can lead to session hijacking, eavesdropping, data exfiltration, and more. Because ARP does not provide any form of authentication, Layer-2 networks are vulnerable without added protections.
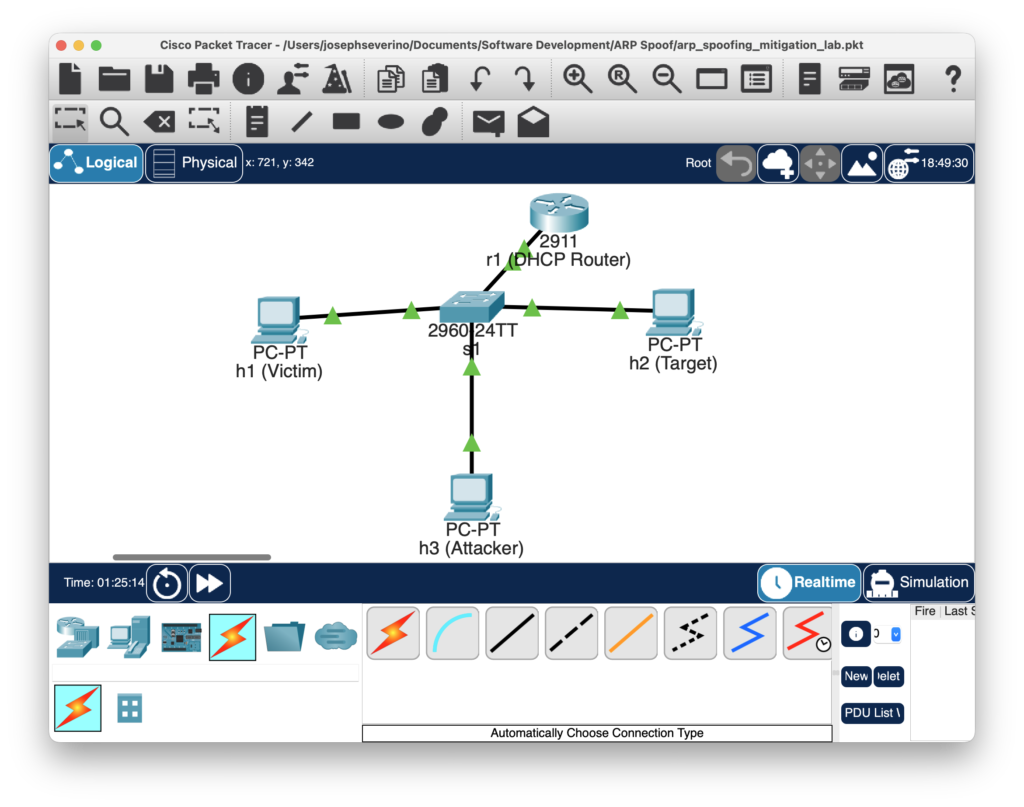
To demonstrate how enterprise networks mitigate ARP spoofing attacks, I recreated the topology in Cisco Packet Tracer using a Layer-2 switch and a DHCP-enabled router. Security features, DHCP Snooping and Dynamic ARP Inspection (DAI) were configured on the switch to prevent spoofed ARP responses.
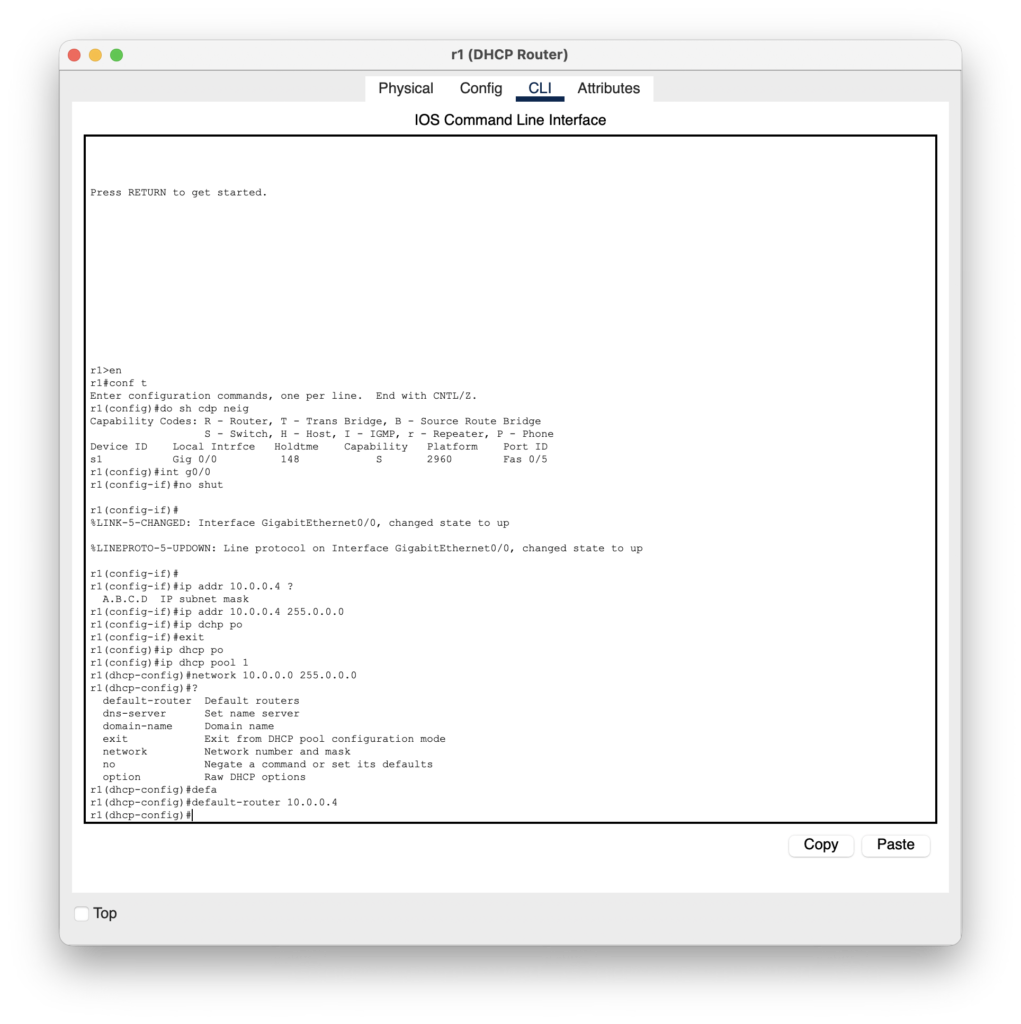
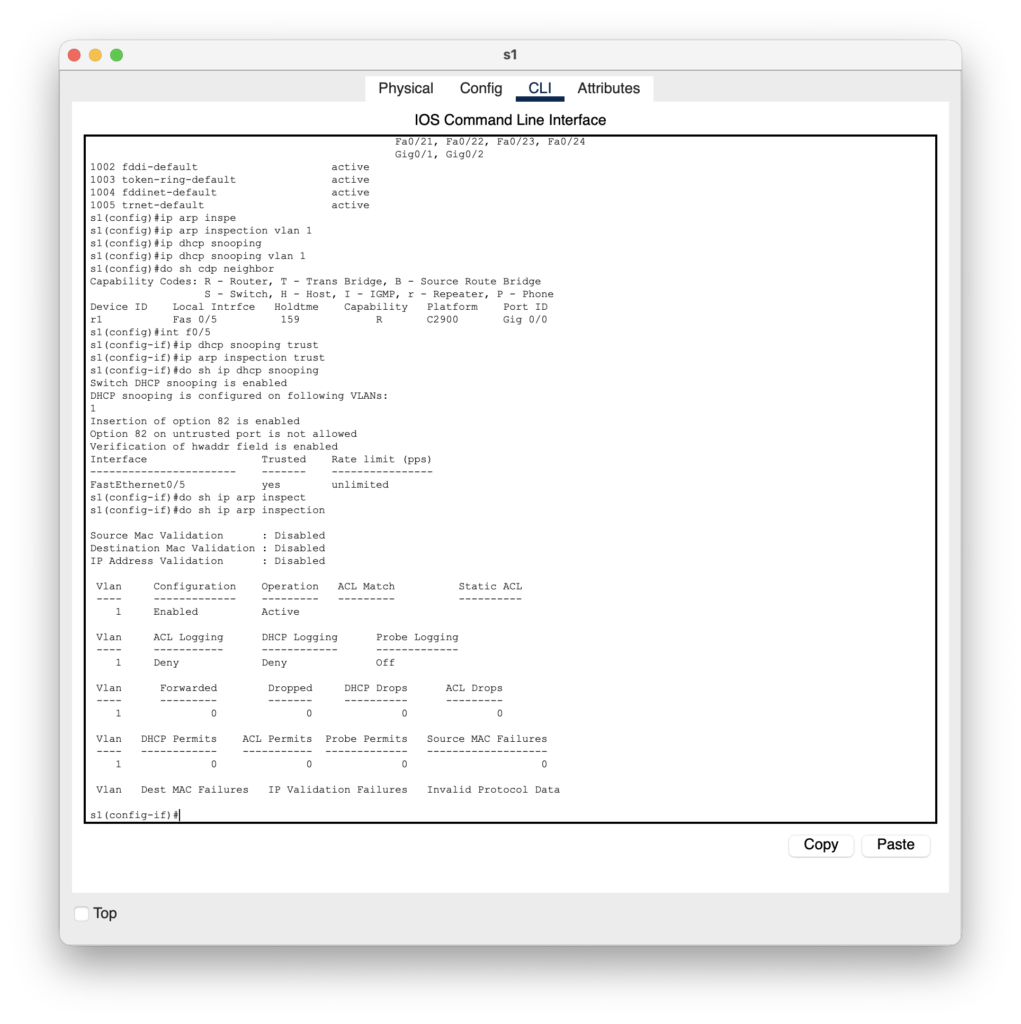
s1 (config)# ip dhcp snooping
s1 (config)# ip dhcp snooping vlan 1
s1 (config)# ip arp inspection vlan 1
s1 (config)# int f0/5
s1 (config-if)# ip dhcp snooping trust
s1 (config-if)# ip arp inspection trustLessons Learned
- While Mininet can simulate the attack, advanced mitigation features such as DHCP Snooping and Dynamic ARP Inspection are not supported. To demonstrate how these are configured in production environments, I recreated the topology in Cisco Packet Tracer.
- Simulated Mininet traffic generates actual packets that can be analyzed in a packet capture. Starting tcpdump prior to the attack allowed for real-world analysis of the effect.
- Manually configuring the IP and MAC addresses on the topology script allowed for the experiment to be deterministic while also repeatable for others.
- The updated ARP tables show just how trusting ARP can be without configuring any security measures.